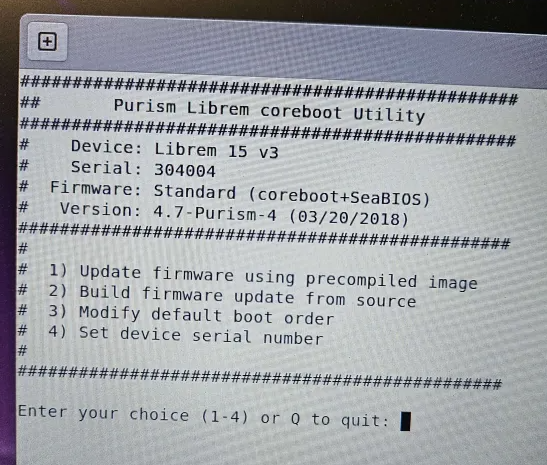
I went with 2: Build firmware update from source.
Accepted defaults.
For git username and email, I just hit enter. I think it ignored that.
It is building now.
Any idea how long this will take?
I went with 2: Build firmware update from source.
Accepted defaults.
For git username and email, I just hit enter. I think it ignored that.
It is building now.
Any idea how long this will take?
@jonathon.hall Are you around to help?
Stuck here.
Going to assume I picked the wrong device for default boot.
Instructions said I could change that. Will reboot to enter bios and pick other device.
I selected 1) since that seems to be the only viable option.
Pretty sure the laptop as a M.2 and a SSD.
OS likely on the one it is not seeing.
The OS is installed on a LUKs partition. That shouldn’t be an issue.
I am stuck.
OK. I went to this menu again, but this time, I just went to change the boot order.
Flashed the bios again. Rebooted. It still won’t boot from hard disk.
What do I do next?
@Eric_Stanek Sorry, looks like you went down a rabbit hole here, wish I had caught this earlier.
For your current state, it looks like GRUB is somehow not completely installed correctly. This would’ve been unnoticed in PureBoot because it does not actually execute GRUB, it just reads the config and then loads Linux itself directly. Now that you’re on SeaBIOS, it’s actually trying to run GRUB, which is not working.
You have a couple of options:
Of course, problems with /boot signatures could come from tampering. If that is a risk to you, then you need to decide whether the system is safe to use before continuing.
For others coming across this, the original problem was that the signature on /boot was invalid - TPM reset shouldn’t have caused this, unfortunately we can’t figure out why it happened since the BIOS has been flashed already. This could be a sign of tampering if that is a risk for you, if you think it was caused by something else you can re-sign /boot. If anybody has this problem in the future (and you are sure it’s not tampering), I’d suggest:
If you want to report a bug in #2 / #3, it’ll be most helpful if you can back up the current ROM and your /boot/kexec* files, and provide any error output (photo of console is OK).
Now that you have flashed Coreboot, you can flash PureBoot over it instead. Choose “Update firmware using precompiled image”, then select PureBoot instead of Coreboot. Keep the power supply connected at all times during the reflashing process.
I am lost on how to proceed. But, not for the reasons described.
I started with a Librem 15v4 with Pureboot and QubesOS preinstalled.
The Librem key was shipped separately for extra security.
I then learned, that it was not possible to use a USB Keyboard/Mouse for security reasons.
That killed my use case (I need a large monitor for my bad eyes) and while I could still connect the external monitor, the laptop would have to be immediately in front of it, so that I could use the laptop keyboard and mousepad. The ergonomics of that were terrible for continuous use for me.
The laptop then sat idle for a few years or so.
Recently, I learned it was possible to upgrade to a newer version of Pureboot / QubesOS, where I should be able to get the USB keyboard and Mouse working, albeit with added security risks - but I am willing to accept those risks.
The changes didn’t work and I ran out of time to resolve them. (I am traveling for months starting in a few days)
So, I went ahead and changed the OS to Fedora, and migrated my data and apps there from my desktop. Murphy’s Law is strong, and my desktop died right after that. Not sure if it is the power supply or motherboard. I will have to wait until spring to figure that out.
Somewhere in there, while installing Fedora on top of PureBoot, I locked myself out changing the TPM password, hence the title of this post.
By now, I had already migrated to the laptop, and could not go back to my desktop.
I really wanted to make sure the BIOS was OK, and hated that I had to use a workaround to select the boot device each time.
With instructions on how to flash the BIOS to Coreboot, I decided to first give it a try on a spare Librem 15v3 first, because I didn’t want to break the currently ‘working’ laptop.
Glad I did that, because It won’t boot now.
I am a smart guy. I consider myself advanced at Linux Sys Admin. Given what I do, I worry I am targeted to be hacked. That’s a way more risky scenario than a ‘drive by malware’ infection. Hence my interest in PureBoot/TPM/Librem Key and QubesOS.
However, it now seems I have 2 options;
or
Extremely Frustrating to say the least.
Sorry. I can’t risk it now.
I am going to limp along with the BIOS boot device selection menu for now, and when I get to the new city, I will buy a standard laptop there.
At that point, I will have 2 laptops, and can risk trying once more with the BIOS update.
Sure, as long as the “standard” laptop fits all of your security needs with your threat model.
What I would really hate to happen, is if this new laptop I end up buying, won’t support Coreboot/Pureboot/QubesOS. Because once the dust settles, I STILL want to try and make QubesOS work.
Any recommendations? I see the ‘approved hardware’ list online, but choices there seem limited or older machines. Maybe I am wrong about that.
To briefly summarize the situation, very few devices support Coreboot/PureBoot with Qubes OS out of the box.
I should add a few more important details:
If you like the idea of acquiring the Librem 14, but do not want to wait for it due to being currently on backorder and an additional 3 week lead time, I have one I am willing to sell if you are interested.
Somewhere in there, while installing Fedora on top of PureBoot, I locked myself out changing the TPM password, hence the title of this post.
Ah, now I see how it got here. PureBoot signs the contents of /boot to provide anti-tampering guarantees. Installing Fedora changed /boot, so the signatures were no longer valid.
PureBoot didn’t want to boot this because /boot had been altered. It can’t tell whether you did this intentionally or the system was tampered. Ordinarily it says this to you and asks if you want to re-sign /boot; if it failed to do this that might be an issue that needs to be fixed, maybe this failed in a particular way that sent you to the recovery shell.
You can have PureBoot’s anti-tampering guarantees with Fedora, you don’t have to use Qubes. Many people like to use both PureBoot and Qubes to get the security benefits of both, but they do have learning curves, and PureBoot works with most Linux distributions.
If you want to wait until you have a second computer to troubleshoot any further, I totally understand. Whenever you would like to continue, I recommend the following:
It’s best to keep the laptop plugged in while flashing, but on the off chance power goes out, it’ll continue flashing on battery. As long as your battery is charged, there is little chance of bricking.
Good points. Thanks for the reminder. Sorry, but a 14" screen is way too small for my eyes, even on a temp basis while I connect to a separate monitor. Getting old sucks.
Thank you again for the feedback. For the little time I had to play with QubesOS on the Librem 15v4, I did notice it was a bit sluggish. That makes sense. QubesOS spinning up VMs for apps is designed for security, not resource efficiency. So, perhaps if I get a new extremely powerful laptop, QubesOS will be much snappier. Of course, I will have lots of research to do to make sure the hardware is compatible etc.
I will revisit this thread in a few weeks when I am settled in the new city. Thanks everyone!