Sorry for my late reply
I hear what you are saying (irwinewade), and I
can inform you that it is my plan to deactivate the WiFi, and only connect the PFSense I have ordered.
Furthermore I will connect all most of my devices to PFSense by cable, and for those devices where Will is the only option, I will setup a “guest user account”.
In regards to my Librem 13, I do connect by cable, using a USB C - Ethernet adapter, which has been working out fine the few times I been online.
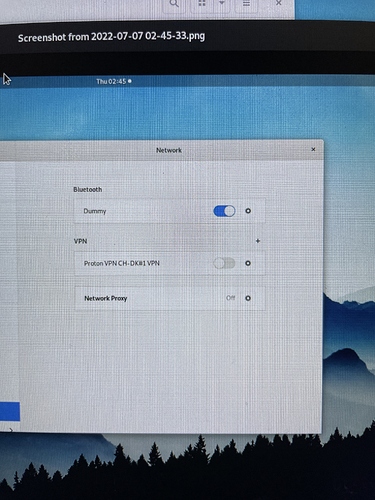
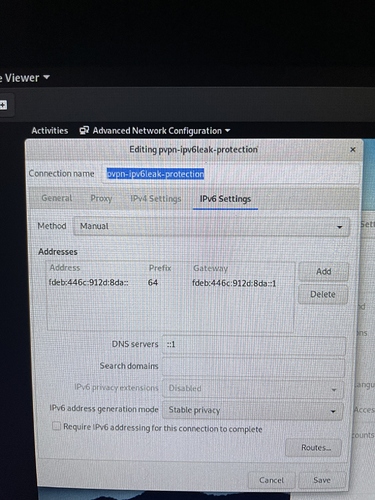
Since last I have been in constant connection with Proton Support, explaining them about the different difficulties I experiencing, and to be honest I am far from satisfied with the Proton Support.
It is not that I am unhappy with the support in general, or that the person I have been in contact with has not been helpful and polite (they have been all that no question). At the same time it is my impression that the company policy, prevents employees the option of admitting any responsibility in regards to their being the slightest possibility that what I am experiencing could be caused be some vulnerability in their software, even though I am experiencing problems with their product on all my different devices at the same time (MacBook Air, iPhone 12 Pro, and Librem 13).
Finally I have made some discoveries in regards to what is happening on my MacBook Air, I have done some research, and due to the fact this exploit is able to control applications like Proton VPN, Malwarebytes, Little Snitch and Wireshark, it narrows down the possibilities.
Given these things I am quite certain this malware must be positioned somewhere in the boot loader (causing it to be undetectable, and unaffected from system resets). From where it has been able to access to the kernel and take control over these different applications.
I am aware this is highly advanced mac security, however I am quite certain this is what has been going on, and should anyone be interested I will be happy to explain/show why that is.