is there a terminal command to check if your system drive is encrypted? it asked me for a password when i installed pureos but I want to check if its working. Also, is luks encryption any good or am I better off using another tool?
Next, I want to learn to code and I want to help companies like pureism, signal (whisper systems), companies who are decent. What language is best to learn for developing Linux (pureos)?
run the blkid command and check the output.
LUKS is the official Linux full disk encryption mechanism, you can’t go wrong with it.
There are other projects like Veracrypt for portable devices.
all it gives me is whats in the dvd drive.
You don’t have /dev/sdX ,/dev/hdX, /dev/nvmeX in the output?
Then try dmsetup info - the output should be something like:
State: ACTIVE
Read Ahead: 256
Tables present: LIVE
Open count: 2
Event number: 0
Major, minor: 253, 0
Number of targets: 1
UUID: CRYPT-LUKS1-7385370f1fbd422c9098cc69f3ac60e2-sda2_crypt
here is the output:
Usage:
dmsetup
[–version] [-h|–help [-c|-C|–columns]]
[-v|–verbose [-v|–verbose …]] [-f|–force]
[–checks] [–manglename {none|hex|auto}]
[-r|–readonly] [–noopencount] [–noflush] [–nolockfs] [–inactive]
[–udevcookie ] [–noudevrules] [–noudevsync] [–verifyudev]
[-y|–yes] [–readahead {[+]|auto|none}] [–retry]
[-c|-C|–columns] [-o ] [-O|–sort <sort_fields>]
[-S|–select ] [–nameprefixes] [–noheadings]
[–separator ]
help [-c|-C|--columns]
create <dev_name>
[-j|--major <major> -m|--minor <minor>]
[-U|--uid <uid>] [-G|--gid <gid>] [-M|--mode <octal_mode>]
[-u|--uuid <uuid>] [--addnodeonresume|--addnodeoncreate]
[--readahead {[+]<sectors>|auto|none}]
[-n|--notable|--table {<table>|<table_file>}]
create --concise [<concise_device_spec_list>]
remove [--deferred] [-f|--force] [--retry] <device>...
remove_all [-f|--force]
suspend [--noflush] [--nolockfs] <device>...
resume [--noflush] [--nolockfs] <device>...
[--addnodeonresume|--addnodeoncreate]
[--readahead {[+]<sectors>|auto|none}]
load <device> [<table>|<table_file>]
clear <device>
reload <device> [<table>|<table_file>]
wipe_table [-f|--force] [--noflush] [--nolockfs] <device>...
rename <device> [--setuuid] <new_name_or_uuid>
message <device> <sector> <message>
ls [--target <target_type>] [--exec <command>] [-o <options>] [--tree]
info [<device>...]
deps [-o <options>] [<device>...]
stats <command> [<options>] [<device>...]
status [<device>...] [--noflush] [--target <target_type>]
table [<device>...] [--concise] [--target <target_type>] [--showkeys]
wait <device> [<event_nr>] [--noflush]
mknodes [<device>...]
mangle [<device>...]
udevcreatecookie
udevreleasecookie [<cookie>]
udevflags <cookie>
udevcomplete <cookie>
udevcomplete_all [<age_in_minutes>]
udevcookies
targets
version
setgeometry <device> <cyl> <head> <sect> <start>
splitname <device> [<subsystem>]
may be device name or (if only one) -u or -j -m
<mangling_mode> is one of ‘none’, ‘auto’ and ‘hex’.
are comma-separated. Use ‘help -c’ for list.
<concise_device_specification> has single-device entries separated by semi-colons:
,,,,
dmsetup info , if you don’t specify a flag it will show you the help menu.
/dev/mapper/control: open failed: Permission denied Failure to communicate with kernel device-mapper driver. Incompatible libdevmapper 1.02.155 (2018-12-18) and kernel driver (unknown version). Command failed.
with a root account or sudo, obviously.
i dont know how to do that.
“sudo dmsetup info” in the terminal.
Doh!
I tried it and got no devices found.
That’s weird. Does your system asks for a boot password, except the user login password?
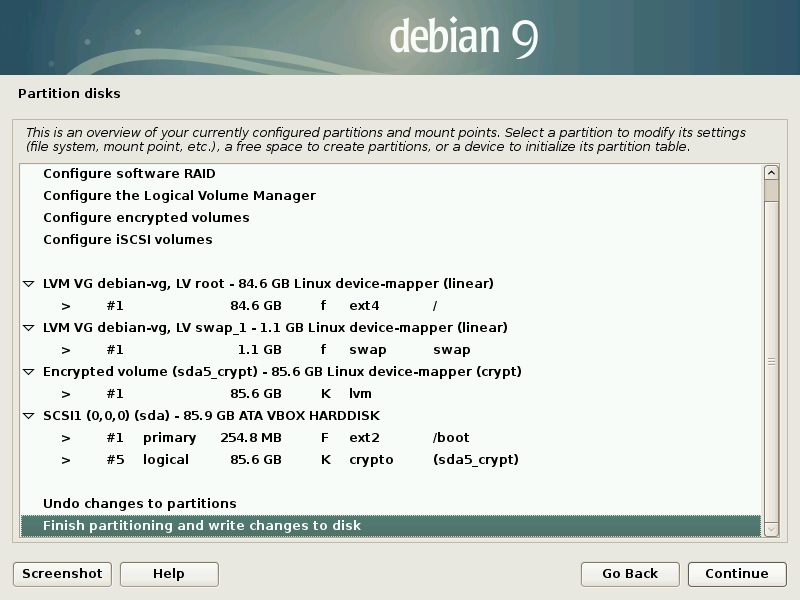
Missing dmsetup or blkid output means something is not right with your encrypted logical volume.
The only password im ever asked for is at login.
So that explains why you don’t have any output in the above commands, you don’t have LUKS.
Obviously, this means that you should reinstall the system to use full disk encryption, since it needs to overwrite all the data. You can theoretically do it without reinstall from another live USB but it’s complicated.
Unless something went horribly wrong with PureOS install (I doubt, this step should be identical to Debian)
you just missed this step when you installed the OS.
Ok, thanks for your help. I did put a password in on install. If I was to access the disc from windows would it ask me for the password? (If it is LUKS enabled).
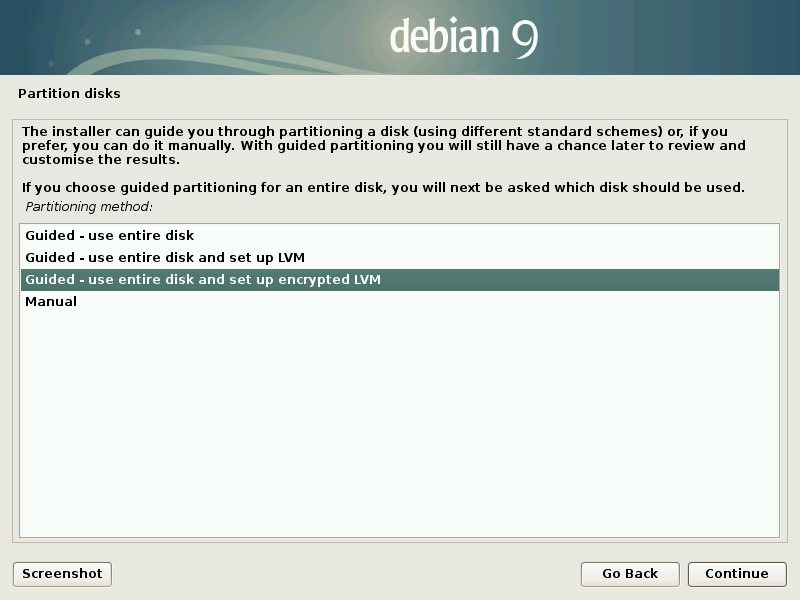
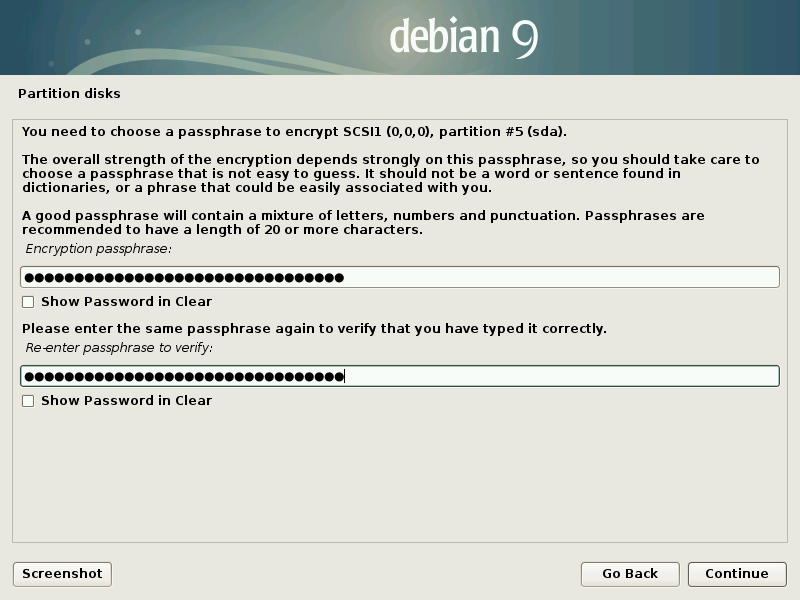
The password during install is just for the user account. The LUKS part is set up during disk partitioning.
There you have an option to use encrypted volume, you can’t really miss it because it’s not hidden under any
menu, it’s just not the default option.
With LUKS Windows cannot access this volume, it’s not a partition type that it can natively mount. Only with 3d party projects like https://github.com/t-d-k/LibreCrypt
I think you are still mixing between simple user account passwords and full disk encryption passphrase, which have nothing much in common and the latter is the only real encryption, user passwords are just for privilege separation.
OK so I’ve put the install disc in, repartitioned the drive, I see an option for ext4 file system and a check box underneath to encrypt, if I tick it 2 boxes appear asking for a passphrase. If I selects LUKS for the filesystem there is no tick box to encrypt and it doesn’t ask for a passphrase. So right now what I see is the opposite of what you’re saying. So now im confused.
What I get is nothing like that, can you try installing it on your system, you can get right up to the partition selection page without making changes to your system. I’ve got the latest version of pureos
This is kind of a trick question. To use a borrowed analogy, what your asking here is “What color of paint should I learn to use if I want to paint electric cars?”
In order to develop a Linux system, you will most likely need to use several different programming languages, along with many non-programming skills and technologies.
As an example, you will need to learn Bash scripting for automating system administration.
You will also need to learn Bourne Shell (sh) for scripting in certain restricted environments like the initrd where you only have Busybox.
You will need to learn C for kernel and device driver development.
But most other native-compiled code will be written in C++ (not the same as C).
If you start building mobile apps, you will need to learn Objective-C (yet another completely different language from C and C++) for iOS development, and Java for Android. You might also need to learn Kotlin or Groovy or some other language that targets the JVM for Android development.
If you’re building web clients, you’ll certainly need to know JavaScript, and maybe a few of it’s dialects, as well as a whole host of other web technologies.
And all through the process, you’ll need to deeply understand the security models and implications of the components you are working with, since that’s the motivation behind Purism and Whisper System’s products. Trust me, understanding infosec is a completely separate (but obviously tightly-coupled) domain of knowledge.
Start with learning Python. As the community is fond of saying, it’s the second-best language for everything. You might end up using it a lot, or not very much at all, depending on what specific projects or components you end up working on. But it’s a very useful and versatile language, and it will teach you how to paint. Once you’ve leaned how to paint, all the other languages are just different colors to paint in.
The best advice I can give you is to just get started. There is no better way to learn than doing, and there’s no better way to get hired than having portfolio of code (Github) for others to see what you’ve done.