Some Intel and AMD CPUs support firmware based TPM(Intel calls it TXT), I wonder where do they save the encryption keys, on motherboard or CPU?
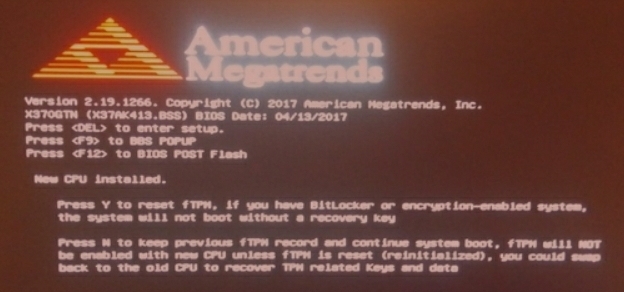
According to the following picture I found on the internet, it seems AMD saves the keys mainly on motherboard, but linked to the CPU somehow:
I just read through the fTPM whitepaper from Microsoft’s researchers for you.
I gather that fTPM leverages a combination of eMMC with replay protection (RPMB) for its state and key storage, plus a write-once secure hardware fuse (which gets a unique key burned into it at the factory).
Given enough entropy, the fTPM (operating in its trusted environment, TEE) will generate symmetric keys to burn into the eMMC controller (part of the same silicon die as the eMMC storage) in order to make authenticated read and write calls. Presumably, this is how it stores the disk en(/de)cryption keys. Check out that whitepaper for more details on the protective mechanisms involved, such as nonces, write counters, timing attack prevention, etc.
The memory, storage, and even processes involved in the “Secure World” execution environment involved in all of this are theoretically invisible to any untrusted code (including the commodity OS) due to the isolation properties of ARM TrustZone. This is called “shielded execution.” The authors admit some compromises were made to get this working in lieu of a discrete hardware TPM (though nothing easily exploitable). For non-ARM architectures, like Intel’s SGX, trusted storage lacks the ability to prevent rollbacks to older versions which may have more vulnerable code.
To get back to your question directly:
where do they save the encryption keys, on motherboard or CPU?
On-CPU storage doesn’t make sense, unless Intel or AMD have also stuck some eMMC enclave into the CPU itself. I’m guessing they are instead using a bus to talk to an eMMC on the motherboard.
Sorry, imperfect answer. But I hope this helps.